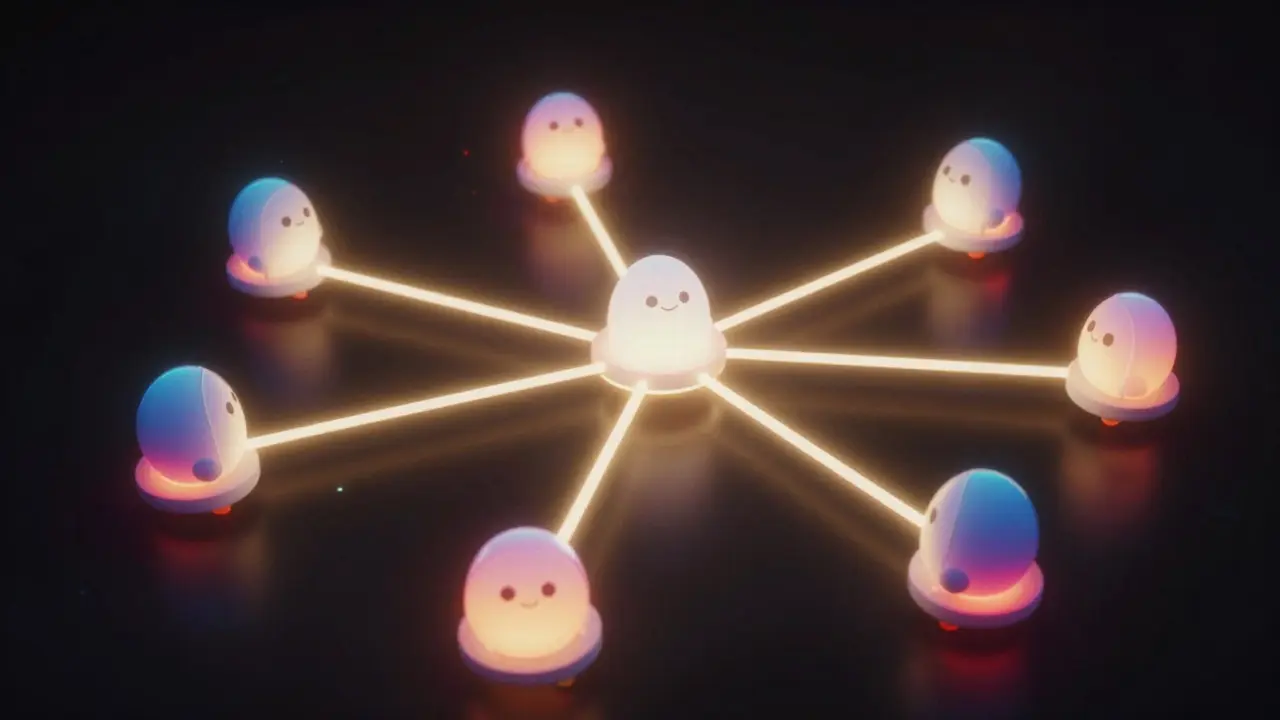
Imagine you are leading an army division. You are surrounded by an enemy city along with four other commanders. None of you can talk directly; you have to send messengers through enemy lines. Here is the catch: some of those commanders might be traitors. If they tell you to attack while others retreat, your army gets destroyed. This isn’t just a war story-it’s the core puzzle behind everything modern blockchain.
This scenario describes the Byzantine Generals Problem, which describes the challenges of achieving reliable consensus in distributed systems where components may fail or act maliciously. Also known as Byzantine Fault Tolerance, it was first formally introduced in 1982 by Leslie Lamport. In today’s world, when we hear about Bitcoin transactions or Ethereum blocks, we are hearing about solutions to this exact ancient computing riddle.
Key Takeaways
- The Byzantine Generals Problem proves that reaching agreement is impossible if one-third or more of participants are dishonest.
- Solutions require Proof-of-Work or advanced mathematical proofs to force alignment.
- Unlike standard server crashes, Byzantine faults assume active deception, not just silence.
- Modern blockchains solved this by adding economic incentives rather than pure code logic alone.
The History Behind the Chaos
To truly grasp the issue, you have to look at the people who defined it. Leslie Lamport, Robert Shostak, and Marshall Pease published their seminal paper "The Byzantine Generals Problem" back in 1982. They weren't talking about Bitcoin then; the technology didn't exist yet. They were looking at aircraft flight control systems and nuclear launch protocols. In those high-stakes environments, a computer crashing is bad, but a computer lying is catastrophic.
The original framework set two critical conditions for any successful coordination:
- All loyal generals must decide upon the same plan of action.
- A small number of traitors cannot cause the loyal generals to adopt a bad plan.
Lamport later received the 2013 ACM Turing Award, essentially the Nobel Prize for computing, largely because he identified that consensus is harder than we thought. He realized that trust cannot be assumed. In a centralized bank, the bank is the general, and everyone trusts them. In a distributed system, there is no single leader. Everyone must agree, even if someone is trying to trick the group.
Why Simple Voting Fails
You might think, "Why can't we just vote?" Most people assume that if 51% of people say 'Attack', the decision is made. That works for crash-fault tolerance, where nodes simply stop working. But in the Byzantine scenario, a node can pretend to be working while sending different messages to different peers. Node A tells Node B to Attack. Node A tells Node C to Retreat. Now B and C disagree, and the system splits.
This is why the math matters. The famous threshold is $3f + 1$. If you have $f$ traitors, you need $n$ total nodes such that $n > 3f$. Essentially, you need two-thirds of the network to remain honest. If there are 10 generals and 3 are traitors ($f=3$), you need at least 10 loyal ones to overpower the lies. Wait-that sounds inefficient. If you only have 4 generals and one is a traitor, you cannot guarantee safety. That is a hard limit. Many enterprise systems fail here because they assume fewer nodes are needed.
From Theory to Blockchain Reality
The leap from academic theory to digital reality happened with Bitcoin. When Satoshi Nakamoto released Bitcoin in 2009, the brilliance was realizing that you don't know who the generals are. In a private meeting room, you pick friends. On the internet, anyone can join. Satoshi used energy consumption-the cost of mining-as the penalty for being a traitor. It turned out that Proof-of-Work was the first practical solution to the Byzantine Generals Problem for open networks.
Instead of counting votes, the network counts work. To write history, you must expend real electricity. As Vitalik Buterin, co-founder of Ethereum, has noted, "Creating economic incentives aligned with honest behavior is better than purely technical constraints." While the underlying mechanics vary, every major chain faces this ghost of Lamport's generals. You see this clearly when comparing the older Proof-of-Work models with newer approaches like Proof-of-Stake.
| Mechanism | Fault Model | Security Basis | Latency |
|---|---|---|---|
| Proof-of-Work (Bitcoin) | Byzantine | Energy Consumption | 10 minutes |
| Proof-of-Stake (Ethereum) | Byzantine | Capital Bonded | < 1 second |
| Paxos / Raft | Crash Only | Leader Election | Milliseconds |
| Tendermint BFT | Byzantine | Cryptographic Signatures | Seconds |
The Hidden Costs of Trustlessness
Implementing these fixes isn't free. Dr. Andrew Miller, a computer scientist at the University of Illinois, critiqued that "Proof-of-work solves the problem but at enormous energy cost." For enterprise users, this is a nightmare. Imagine running a supply chain ledger where you need fast confirmation, but the energy bill rivals a factory's power draw. That is why we saw a shift toward Delegated Proof-of-Stake and other variations during 2022 and 2023.
Ethereum's "Merge" in September 2022 was a massive migration from work to stake. The result? Transaction processing dropped from roughly 15 seconds of latency to under one second, while keeping security guarantees similar. However, the challenge shifts from hardware to software. Developers report that implementing Practical Byzantine Fault Tolerance (PBFT) takes months longer than standard crash-tolerant setups. A 2022 Stack Overflow survey showed that 78% of developers find understanding these requirements the hardest part of distributed system design.

Where This Matters Beyond Crypto
You might think this is just for geeks trading tokens, but the applications are wider. Look at NASA's Artemis program. Their documentation specifies that all critical spacecraft control systems must implement Byzantine Fault Tolerance with the $n > 3f + 1$ configuration. Lunar missions cannot afford to wait for a server fix-up if a signal gets corrupted by radiation.
In the automotive sector, 78 of the top 100 suppliers are deploying these protocols for vehicle-to-vehicle communication. ISO 21448:2022 safety standards now mandate checking for malicious spoofing in autonomous driving systems. Your car needs to know if another vehicle is actually braking or if a hacker is pretending to brake to confuse its sensors. The Department of Homeland Security also mandated BFT implementations for new US electrical grid control systems by 2026 per Cybersecurity Directive 2023-04. We are moving from abstract algorithms to physical safety systems.
Current Developments and Future Proofing
As we move deeper into 2026, the conversation has shifted toward quantum threats. IBM Research announced a quantum-resistant protocol called Q-BFT in June 2023. Traditional cryptography could eventually fall to quantum computers, breaking the signatures that prove loyalty in a network. New algorithms focus on reducing message complexity from quadratic growth to linear growth. Protocols like HotStuff, originally developed by Facebook's Diem team, are now standard in projects like Chia Network and Libra derivatives because they handle thousands of nodes better than older methods.
The market for these technologies is exploding. MarketsandMarkets projects the BFT technology market to grow from $2.1 billion in 2023 to nearly $10 billion by 2028. Enterprises aren't just experimenting anymore; they are relying on this technology for financial settlement layers. Yet, the fundamental lesson remains constant: you cannot achieve perfect agreement without paying a cost in time, energy, or money.
Frequently Asked Questions
What exactly is the Byzantine Generals Problem?
It is a theoretical model describing how distributed computer systems can reach a consensus when some participants (nodes) might be faulty, disconnected, or acting maliciously. It highlights the difficulty of ensuring all honest parties agree on a single course of action without a central authority.
Why is it called "Byzantine"?
The term comes from the Eastern Roman Empire, historically known for political intrigue and complex alliances. In computer science, it became shorthand for arbitrary failure modes-situations where a component behaves unpredictably or deceptively, rather than just stopping completely.
Can you solve the problem with a simple majority vote?
No. A simple majority fails because traitors can lie to different groups. To solve it mathematically, you typically need more than two-thirds of the network to be honest (specifically $n > 3f + 1$ where f is the number of failures). Without meeting this ratio, consensus is impossible.
How does Bitcoin solve this?
Bitcoin uses Proof-of-Work. Instead of trusting who is voting, the network trusts the amount of energy spent to create a block. It creates a financial disincentive to lie because attacking the network requires so much power that it is economically irrational for most actors.
Is this relevant for companies using non-crypto databases?
Yes. While typical business databases use simpler crash-tolerance (like Paxos), mission-critical infrastructure like power grids, space navigation, and autonomous vehicles are increasingly adopting Byzantine Fault Tolerance to protect against insider threats or cyberattacks.
Adriana Gurau
April 1, 2026 AT 20:04Most people fail to grasp the sheer magnitude of coordination required here without realizing the underlying risks.
The assumption of malicious actors changes the entire mathematical framework compared to simple crash failures.
It is frustrating seeing casual readers skip over the Lamport paper details entirely.
One needs to understand that trust is not a given variable in these equations.
I hope the next generation of engineers stops relying on vague analogies about wars.
Technical precision matters far more than storytelling in this context.
We are dealing with infrastructure that powers global economies after all.
Ignoring the nuance leads to catastrophic system failures down the road.
This is why I advocate for rigorous study before building any ledger.
Otherwise you are just gambling with distributed state.
Please take the time to read the original documentation yourself instead of summaries.
We cannot afford sloppy implementations in critical sectors anymore.
June Coleman
April 1, 2026 AT 23:20You really think everyone is going to sit down and calculate hash rates manually.
That is adorable in a way that almost works.
But seriously the energy costs alone are enough to deter many projects.
We need to move past the brute force mining model soon enough.
Proof-of-Stake seems like the next logical step despite the risks.
Just don’t expect the network to fix itself while you sleep.
I would love to see more discussion on the actual governance mechanics though.
Otherwise we are just shifting problems to a different layer.
Keep reading and stay skeptical of the hype machine surrounding this tech.
Emily 2231
April 2, 2026 AT 06:27The government controls these protocols regardless of what the white papers claim.
Deep state actors manipulate the node distribution to maintain power.
They want you to believe in decentralized trust while they watch your transactions.
We must resist the encroachment of foreign entities on our domestic grids.
National security is at risk when external servers validate our ledgers.
Trust no one who claims to have the final word on protocol upgrades.
Always verify the source code against official archives personally.
Corruption happens at every layer of the system architecture.
Beware of the quiet updates changing the rules of engagement.
Patriots should build sovereign chains independent of foreign servers.
Robert Coskrey
April 3, 2026 AT 19:11While the concerns regarding security are valid, the mathematical proofs provide robust guarantees.
Byzantine Fault Tolerance remains a cornerstone of reliable distributed computing today.
It is essential to distinguish between theoretical limits and practical implementation issues.
The $3f + 1$ threshold offers a clear boundary for system designers to follow.
Ignoring these constraints results in unstable networks prone to partition attacks.
Further research into asynchronous consensus continues to advance the field significantly.
Thank you for highlighting the importance of Leslie Lamport contributions.
We must continue to respect the rigor required in these protocols.
Suvoranjan Mukherjee
April 4, 2026 AT 16:34Incredible breakdown of the PBFT versus PoW dynamics for enterprise adoption.
Latency constraints in Tendermint BFT are much tighter than standard Bitcoin blocks.
We see massive gains in TPS when moving from proof-of-work architectures.
Capital bonded stakes offer better alignment for validator nodes in the ecosystem.
Quantum threats mentioned are a real vector for future vulnerability assessment.
I appreciate the inclusion of Q-BFT discussions in this context.
Developers need to focus on cryptographic agility now more than ever before.
Stack Overflow surveys highlight the difficulty of implementing these logic flows correctly.
Message complexity reduction is vital for scaling to thousands of active validators.
JERRY ORTEGA
April 5, 2026 AT 15:37yeah i guess its true though the math checks out for the most part.
i was thinking about how cars handle spoofing signals too.
looks like we got a few layers of protection added recently.
just hope the battery life on sensors doesnt drain fast.
seems like a solid read overall.
thanks for putting the effort into the formatting here.
not gonna lie i learned something new today.
probably gonna check out the iso standards later.
shubhu patel
April 7, 2026 AT 15:32The evolution of consensus mechanisms really captures the essence of distributed systems design.
We cannot ignore the historical context that preceded the digital age in computing.
Many developers overlook the foundational work done in aerospace engineering fields.
Safety critical systems demand higher standards than typical web applications require.
When we talk about fault tolerance we must consider the human element involved too.
A network node behaving maliciously is akin to a rogue pilot in flight control systems.
The economic incentives described in Bitcoin solved a lot of initial adoption friction.
Yet Proof-of-Stake introduces new vulnerabilities that remain largely untested at scale globally.
Energy consumption is a valid metric but it carries significant environmental baggage.
Transitioning to stake models requires careful governance to prevent centralization issues occurring.
The shift towards quantum resistance indicates how quickly threat landscapes evolve rapidly.
Traditional cryptography may soon face obsolescence due to advancing hardware capabilities worldwide.
Industries like automotive integration show the practical necessity beyond cryptocurrency tokens.
Vehicle-to-vehicle protocols rely heavily on these Byzantine assumptions for safety operations.
Ultimately the cost of trustlessness defines whether a system survives long term reliably.
Arlen Medina
April 9, 2026 AT 06:08You are clearly missing the point about how simple voting fails completely.
Traitors dont need to coordinate with anyone to break the system entirely.
Any node lying to different peers destroys the consensus guarantee immediately.
This isn't just theory it is basic logic that you seem to ignore here.
Don't tell me you haven't checked the n greater than three f plus one formula.
If you cant do the math then stop posting about distributed systems.
The threshold requirements are non-negotiable for any secure network setup.
Misunderstanding this puts entire financial layers at risk of collapse.
Read the actual paper instead of relying on blog summaries.
Your current level of understanding is insufficient for this topic frankly.
Taylor Meadows
April 10, 2026 AT 00:35This makes me feel so lonely knowing how much deception is possible online.
Every transaction feels like a gamble against unknown bad actors constantly.
I worry that my privacy is being eroded by these constant validation checks.
There is a deep sadness in having to trust machines over people.
The fear of betrayal hangs over every digital interaction we make.
How do we rebuild genuine connection when algorithms decide truth?
It hurts to realize that loyalty is calculated in code and electricity.
We have sacrificed emotional bonds for cold verification processes sadly.
vijendra pal
April 11, 2026 AT 23:30this stuff is so hard to understand lol 😅
david head
April 12, 2026 AT 11:43nice work man 👍
really helps clarify the differences between the consensus types.
Patty Levino
April 13, 2026 AT 11:32I understand the frustration with implementing such complex systems for beginners.
It takes patience to learn the nuances of Byzantine Fault Tolerance properly.
Everyone starts somewhere and asking for help is always a good choice.
The community tends to be supportive when technical details are explained well.
Just take your time exploring the resources listed in the article carefully.
You will find your footing once the concepts click into place eventually.
Alexandra Lance
April 13, 2026 AT 14:10Another day another algorithm designed to control the masses 🤡
Who decides which nodes are loyal in this grand scheme of things.
The elites will always find a way to bypass the math eventually.
We are just pawns in a game played by invisible hand controllers.
Enjoy your little blockchain utopia while it lasts for sure.
Wake up and smell the centralized coffee served by big banks.
I doubt they care about your distributed dreams honestly.
Stay vigilant because the end game is always consolidation anyway.
History repeats itself in code form with predictable outcomes always.
They profit from your confusion while selling you false freedom.
Lauren Gilbert
April 14, 2026 AT 06:33Trust is a fragile commodity in any society built on digital interactions.
We often forget that mathematics cannot solve purely political disagreements alone.
The generals problem is a metaphor for our modern lack of shared reality.
Every blockchain attempt is essentially a plea for agreement without leaders.
History teaches us that centralized power corrupts almost every single time.
However decentralization creates a vacuum where new hierarchies inevitably emerge.
Miners became the new generals controlling the fate of transaction history.
Stakeholders now vote with their wealth rather than their moral compasses.
Many wonder whether this is truly freedom or simply a redistribution of influence among the rich.
The narrative of permissionless access hides behind complex entry barriers always.
Technical elegance often masks the social inequalities embedded in code design choices.
We must ask who benefits most from high energy cost consensus methods globally.
Perhaps the solution lies in hybrid models balancing efficiency and security.
The philosophical implications of machine agreement outweigh the technical hurdles.
Future generations will judge us on how we handled this digital transition era.
Sonya Bowen
April 14, 2026 AT 13:34Focus on the core constraints before worrying about advanced variants.
Understand the base case thoroughly before optimizing for performance.
Security should never be compromised for speed in mission-critical systems.
Review the ISO standards referenced for additional compliance guidelines.
Implementation details vary widely across different industry verticals.
Carol Prates
April 16, 2026 AT 13:32OMG the energy costs are absolutely insane for Proof-of-Work chains!!!
Why would anyone choose to burn that much electricity for transactions??
Ethereum merging to stake changed everything for the better imo.
Can we finally have faster speeds without killing the planet??
The table comparison really drove the point home for me.
I hope all industries follow suit soon for sustainability reasons.
This is huge news for the environment and tech alike!!
Let’s move forward with green solutions from here on out!
Hugo Lopez
April 17, 2026 AT 08:57I completely agree with the excitement regarding faster speeds now 😊
Lower latency is crucial for real-time applications in finance.
We need to encourage innovation that prioritizes ecological impact.
Great job highlighting the shift toward Proof-of-Stake mechanisms here.
Looking forward to seeing more adoption of these safer methods.
Together we can build a more sustainable digital future for everyone 💪.
Carmelita Gonzales
April 18, 2026 AT 18:53Important considerations for cross-border protocols.
Cultural exchange of tech standards is beneficial.
Respect local regulations when deploying.
Ensure privacy is maintained at all times.
Grateful for the detailed information provided.
Adriana Gurau
April 19, 2026 AT 00:01The market growth projections seem optimistic without sufficient regulatory clarity.
Compliance frameworks are lagging behind technological advancement significantly.
Investors should exercise caution before committing capital to BFT projects.
Regulatory uncertainty poses a greater risk than technical failure currently.
We need transparency from development teams regarding governance structures.
Without oversight these systems become vulnerable to manipulation easily.
My recommendation is to wait for clearer legal precedents to emerge.
Nicholas Whooley
April 19, 2026 AT 23:31The outlook for distributed consensus technology remains incredibly positive.
We are witnessing the dawn of a new era in digital collaboration.
Challenges present opportunities for meaningful innovation and growth.
Faith in open protocols drives progress forward steadily.
Let us continue to explore the possibilities with enthusiasm and rigor.
Thank you for bringing attention to these vital concepts today.